For years, many virtualization decisions were made almost by inertia. However, the current landscape has pushed many companies to revisit something that once seemed settled: whether it still makes sense to stay on the same platform or whether the time has come to explore alternatives that offer more technical control, less vendor dependence, and a more predictable cost structure.
In that context, Proxmox VE has gone from being seen as a valid option for small environments or labs to becoming part of much more serious discussions within systems, operations, and infrastructure teams. The key point, however, is not just the potential savings. When a CIO or CTO considers a migration away from VMware, the relevant questions are not only financial. The real questions are about risk, continuity, high availability, backups, performance, compatibility, and operational readiness.
And that is the most important point: migrating from VMware to Proxmox VE is not simply about changing hypervisors. It is about reviewing the virtualization platform as a whole.
Below, we look at the questions technical leadership teams typically ask before taking on a migration like this, and why the answer cannot be reduced to a simple feature-by-feature comparison.
The first question is not “how much will we save?” but “what risk are we taking on?”
When evaluating a migration, savings usually get attention first. That is normal. But in enterprise projects, that is rarely the deciding factor. The conversation quickly shifts to other concerns: how much downtime there will be, how operations will be protected, what will happen to high availability, how backups will be handled, and how much real room there will be to roll back if something goes wrong.
In other words, the real debate is not whether Proxmox VE costs less, but whether it can support operations with the required guarantees.
That shift in perspective also explains why a well-planned migration should not be treated as a purely technical project. In reality, it affects business continuity, change management, operational procedures, and recovery architecture. Once it is understood that way, the decision stops being a reaction to market conditions and becomes a platform project.
How much downtime am I going to have?
This is almost always the first question that comes up in any serious meeting.
The correct answer is rarely “zero.” It depends on the workload type, the migration method, the available maintenance window, and the organization’s tolerance for risk. In export-import scenarios, each virtual machine will usually require downtime. For critical services, on the other hand, the sensible approach is to organize the work in waves, with prior testing, functional validation, and a rollback plan that exists in practice, not just on paper.
The lesson here is fairly simple: migrating everything at once is usually not a good idea. The right approach is to classify workloads by criticality and dependencies. An auxiliary VM, a development environment, or an internal application does not require the same treatment as a transactional database, an ERP system, or a platform serving end customers.
That initial segmentation often makes the difference between an orderly migration and a painful one.
Can high availability be maintained in Proxmox VE?
Yes, but it is important to explain what that really means.
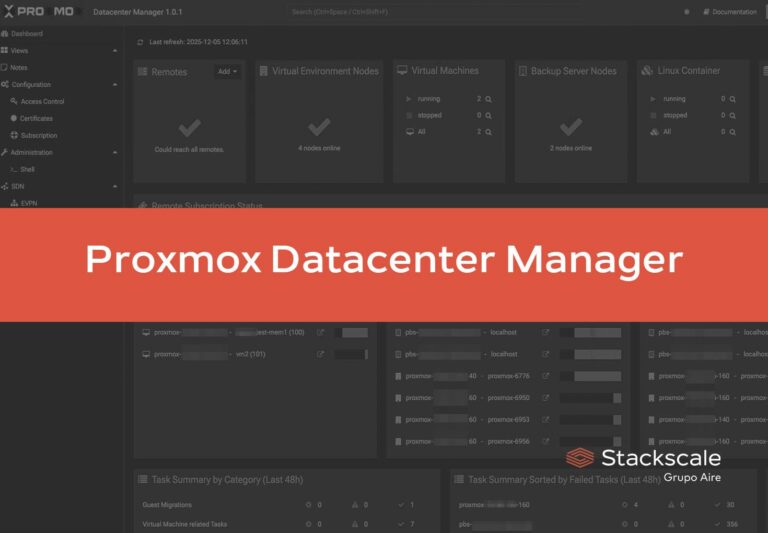
Proxmox VE includes clustering and high availability capabilities, and its HA model allows virtual machines or containers to restart automatically on other healthy nodes when a failure occurs. That said, this does not mean high availability appears by magic. It also depends on cluster design, quorum, networking, and storage. In other words, HA is not something you simply switch on. It is something you build.
This fits very well with the way Stackscale approaches these projects: not as a checklist of isolated items, but as a combination of infrastructure, operations, and recovery objectives. In practice, the platform has to align with technical, operational, and business requirements, and Proxmox VE can fit into multi-node clusters with high availability, integrated backups, and different storage options.
What risks are involved in a V2V conversion?
In any VMware-to-Proxmox project, V2V (virtual-to-virtual) conversion comes up sooner or later. And here it is important to avoid two very common mistakes: assuming everything will be trivial or assuming everything will be problematic.
Most issues tend to be concentrated around the same areas:
- drivers and tools installed in the guest operating system
- BIOS versus UEFI differences
- network interface configuration
- disk performance after conversion
- specific drivers in Windows environments
- services that depend on settings inherited from the previous environment
These are not exotic risks. They are normal risks.
That is why the most solid migrations almost never start with a large-scale wave. They start with a pilot. A pilot with representative machines, different operating systems, different workload profiles, and applications that make it possible to validate not only that the VM boots, but that the application continues to work as expected.
That pilot helps refine templates, document exceptions, identify incompatibilities, and build a realistic decision matrix. In practice, it turns the migration into a repeatable process.
What about backups and Disaster Recovery?
This is where many organizations realize they are not just reviewing a hypervisor, but their entire recovery strategy.
Proxmox VE can integrate natively with Proxmox Backup Server (PBS), which provides incremental backups, deduplication, integrity verification, and synchronization options between locations. All of this makes it possible to design more efficient policies in terms of both storage consumption and network impact.
But beyond the specific tool, the underlying issue remains the same: copying is not the same as recovering.
If a restore has not been tested, the backup should not be considered validated. That is why a well-designed migration requires defining RPO (Recovery Point Objective) and RTO (Recovery Time Objective) targets from the outset, along with retention policies, restore procedures, and post-recovery functional validation. Recovering a virtual machine is not enough; you need to verify that the service actually comes back online and works as expected.
This approach is fully aligned with Stackscale’s broader view of Disaster Recovery: prioritize resources, define RTO and RPO, test the plan regularly, and understand that there is no universal design. Recovery architecture must be adapted to each company’s level of criticality.
Is Proxmox VE suitable for enterprise environments?
The short answer is yes.
The useful answer is yes, as long as it is treated as an enterprise platform and not as a “cheap hypervisor” to which everything else will be added later.
That means designing the cluster correctly, defining the storage strategy, setting up roles and permissions with RBAC (role-based access control), strengthening hardening, ensuring monitoring, organizing networks properly, and documenting operational and recovery procedures.
It also means relying on an infrastructure layer that supports that design. In Stackscale’s case, we link Proxmox environments to cloud infrastructure capabilities such as dedicated compute nodes, network storage, synchronous storage, integration with a network independent from the virtualization environment, and multi-data-center architectures for continuity and backup.
That becomes especially relevant when the organization is not just trying to “move away from VMware,” but to use the migration as an opportunity to leave behind a more organized, more stable, and more predictable platform for the years ahead.
Basic checklist for a VMware → Proxmox VE migration
| Phase | Checkpoint | What to review |
|---|---|---|
| Project governance | Scope and ownership | Define sponsor, technical team, success criteria, and communication plan |
| Inventory | Workload discovery | Inventory VMs, dependencies, networking, storage, operating systems, and criticality |
| Classification | Segmentation | Separate services by criticality: low, medium, high, and mission-critical |
| Target design | Proxmox VE cluster | Size nodes, quorum, HA, management network, and storage network |
| Target design | Storage | Choose between local, network, or synchronous storage based on RPO/RTO |
| Security | Access and hardening | Review RBAC, segmentation, logs, and monitoring |
| Pilot | Initial selection | Choose representative VMs to test compatibility, boot, networking, and performance |
| Pilot | Functional validation | Confirm that applications work correctly after conversion |
| V2V | Compatibility | Review BIOS/UEFI, drivers, Windows controllers, and disk/network behavior |
| Waves | Planning | Group machines by dependencies and criticality; avoid simultaneous mass migration |
| Rollback | Real rollback plan | Document and test rollback by service type |
| Backup | Policy and restore | Define retention, repositories, and periodic restores with functional validation |
| DR | Secondary location | Evaluate recovery in another zone or data center if applicable |
| Post-migration | Stable operations | Review usage, incidents, capacity, and procedures before project closeout |
Success is not “it boots,” but “it runs well weeks later”
Many companies measure the success of a migration on the day the virtual machines boot on the new platform. But that moment only closes one phase of the project. By itself, it does not prove the migration was successful.
The real test comes later: when operations remain stable, backups restore correctly, monitoring provides useful visibility, teams have clear procedures, and the business no longer feels that every change could trigger an incident.
That is when it becomes clear whether the organization carried out a reactive migration just to get away from a commercial problem, or whether it used the transition to genuinely strengthen its platform.
In many cases, the most important savings do not come only from licensing. They come from reducing complexity, avoiding operational mistakes, and building a more predictable infrastructure, both in terms of costs and continuity.
Frequently asked questions
Can Proxmox VE replace VMware in an enterprise environment?
Yes, as long as the migration is approached as a complete platform project, including cluster design, storage, backup, security, and operations.
Does high availability in Proxmox VE work the same way as in VMware?
It should not be treated as an automatic one-to-one equivalent. Proxmox VE supports HA, but its effectiveness depends on cluster design, quorum, networking, and storage.
What usually causes the most problems in a V2V migration?
Typically, drivers, BIOS/UEFI settings, networking, storage, and certain Windows-specific drivers or dependencies.
Is a pilot required before migrating?
In enterprise environments, it is highly recommended. It helps validate compatibility, performance, procedures, and rollback before touching critical workloads.
What role do backups play in this type of migration?
They are essential. A migration forces you to review not only how backups are created, but how they are restored, how long recovery takes, and whether they truly meet the defined RPO and RTO objectives.